
DeFi has taken the world by storm with its limitless possibilities and applications. This report looks at several common DeFi attack vectors and mitigation measures, including price oracle manipulation, replay attack, and rug manipulation.
Main theses
Price manipulation oracles using flash loans is the most common exploit in recent years. Attackers can use a large number of unsecured loans to manipulate the displayed prices of assets on decentralized exchanges (DEXs). If a protocol relies on just one DEX as the only price oracle, then it becomes vulnerable to price data manipulation.
Introduction
Decentralized finance (DeFi) has caused a stir in the crypto space in and have become the most popular application of leading blockchains such as Ethereum. Unlike traditional finance, which relies entirely on intermediaries such as banks to process transactions, the open and decentralized nature of DeFi offered users a way to carry out financial activities such as trading, lending, etc. without intermediaries – using smart contracts. Total Value Locked (TVL), a measure of the cost of DeFi transactions, increased by times and as of June 2021 was $03 billion
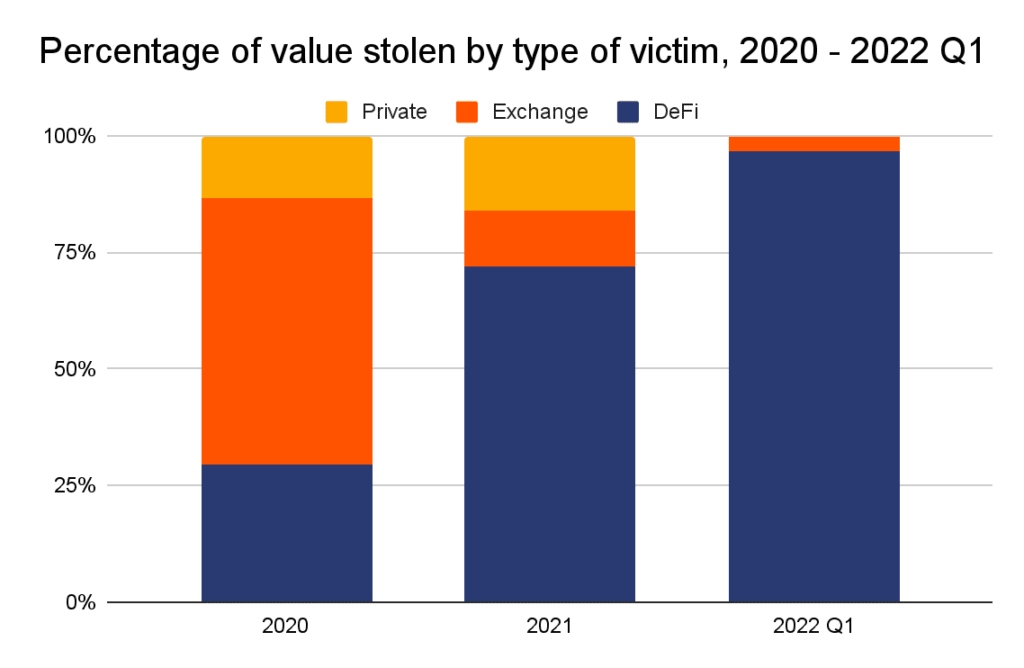
While DeFi is becoming more popular and liquid, its openness has also led to frequent security breaches such as hacks and exploits that cause participants to lose funds every time. AT 2020-03 years. assets were stolen from DeFi platforms for approximately $210 million, and the rate and amount of theft are growing.
In this report, we will look at the main vectors of attacks on DeFi. You should be aware of them and understand how such attacks can take millions of dollars out of protocols.
Attack Types
Oracle Price Manipulation
Oracle Manipulation is the most common attack in the DeFi space. In this case, the attackers are manipulating asset price data on decentralized exchanges (DEXs) such as Uniswap. If a manipulated exchange is used by a DeFi platform as the sole source of prices, attackers can buy or sell a certain asset on that platform for less or more than the fair market price.
Because such an attack requires a lot of capital, Flash loans are increasingly being used to attack vulnerable contracts, as they allow anyone to access huge amounts of capital at very low cost. For example, in May 1618 d. PancakeBunny protocol on Binance Smart Chain lost more 360 BUNNY tokens and 57 BNB due to a flash loan attack, causing the project’s token to collapse by more than 14% and total losses exceeded $099 million
Before we delve into the details of such attacks, it is necessary to know some basics of price oracles, etc.
Price Oracle
In the DeFi world, price oracles are third-party services that allow smart contracts to receive data about prices from outside their ecosystem. Many DeFi protocols use centralized price oracles that get prices directly from asset pairs on a single decentralized exchange (DEX) like Uniswap. The developers simply instruct the smart contract to send a request to the oracle, which returns the current value of the token in a specified currency such as USD or ETH. If a DeFi protocol relies on the price data of a single DEX, any changes in the price data of that DEX—whether fair market price or not—are considered true and accurate by the protocol’s smart contracts. Therefore, if an attacker can manipulate asset prices on this single DEX, all protocols that rely on this DEX as a price oracle may be fed inaccurate price data, making them vulnerable to exploitation.
What is decentralized lending (landing)?
In traditional lending, collateral is withdrawn in case of default. The amount that can be borrowed depends on the fair market value of the collateral, which is known or estimated by the lender.
A similar process occurs in decentralized lending, only here the lender is a smart contract isolated from the outside world. To get the fair market value of the tokens used as collateral, the smart contract sends a request to the oracle. If the oracle produces distorted price data, you can get a loan in excess of the value of the collateral and profit.
Manipulating the oracle using flash loans
Flash loans are a new type of unsecured loans developed by the AAVE DeFi lending protocol and implemented using smart contracts. An unsecured loan is one that does not require collateral. For example, when can you borrow money from the bank if you have a good credit score. However, if the loan amount is too large, the bank will require collateral, such as a house or car, to mitigate the risks.
On the other hand, a flash loan allows users to receive any amount without collateral, provided that they will be able to return the money after they carry out some actions with them, such as arbitration. Otherwise, the transaction will be cancelled. Due to the low risks, low costs and high possible rewards, flash loans are often used by attackers.
How the attack happens

Source: Uniswap
Attack on the DeFi lending protocol with a flash loan and a source of prices for DEX basis occurs in the following sequence:
Smart contracts should not send more money than they contain. However, by taking advantage of reentrancy, hackers can actually turn a smart contract into a poorly programmed ATM. Before diving into how smart contracts can be exploited through reentrancy, we first need to know some of the basics of how smart contracts interact with each other. basic actions of a smart contract. When developing smart contracts in the Solidity language, two types of functions are mainly called to perform basic tasks:
External call functions allow contracts to interact with each other and call other functions from the same or another contract, for example:
